Social Engineering: How Cybercriminals Use Your Emotions to Hack You

In the new episode of I Am Hacked, RT Documentary carries out an experiment to show how little people active on social media know about the risks related to cyber activities and the ways to mitigate them. Meanwhile, hackers resort to devious social engineering tactics to get hold of our personal data and money. Why do we remain so complacent? Tune in to the premiere of the third episode of I Am Hacked on Monday to find out!
In recent decades the world wide web has become an integral part of human endeavour. We work and study online, go shopping, make friends. Our whole lives seem to be packed in our smartphones and laptops.
While enjoying all the perks of the online world, we tend to forget that it hides considerable risks and dangers, just like the real world. Moreover, we tend to forget that just like in the real world, we look around before crossing the road; in the online world, we need to follow certain precautions that will guard us against its dangers.

Today, the pace of online life seems to be keeping up with that of the real one. The pace often becomes so speedy that people don't have the time to process what is going on thoroughly. As a result, internet users are regularly being distracted. They are getting so many notifications from their social media, from their emails that they lose the ability to check where these requests are coming from, which gives hackers wide room for manoeuvre. And they tend to use it to their best advantage.
How do they get it?
When asked where hackers get our personal data from, most participants in our experiment had little to say. Meanwhile, the answer turns out to be pretty simple: first of all, they can get loads of personal data from the proverbial digital footprint. In Layman's terms, cyber wrongdoers don't even need to hack your accounts to access basic information about your life: your preferences, movements, address etc.
"All your geotags, photos you post on Instagram, opinions you share on Facebook and so on – all this in the future can somehow form your, let's say, psychological portrait. What kind of food you like, where you like to go, what kind of music you listen to, when you get sick, and so on," says Ivan Botanov, a @STRESSOID penetration tester.
"There are more and more devices around; people use the internet more and more often, register in a bunch of different systems – and no one checks these systems. You have registered somewhere, left something, and in the end, it will lie and wait in the wings."
One of the most likely reactions to hearing Ivan's arguments seems to be scepticism. "Well, they will open my profile, see my photos, maybe find my phone number and email. So what? Nothing will happen."
"People tend to think that if this application is on an iPhone, then it is safe, then it can be used", says Rustem Khayretdinov, growth director at BI. Zone. "But, as experience shows, this is not the case. These very often become attack vectors".
If the same people who are sceptical about personal data associated risks are shown in an experimental model how easily other users can get their personal data, their attitudes change.
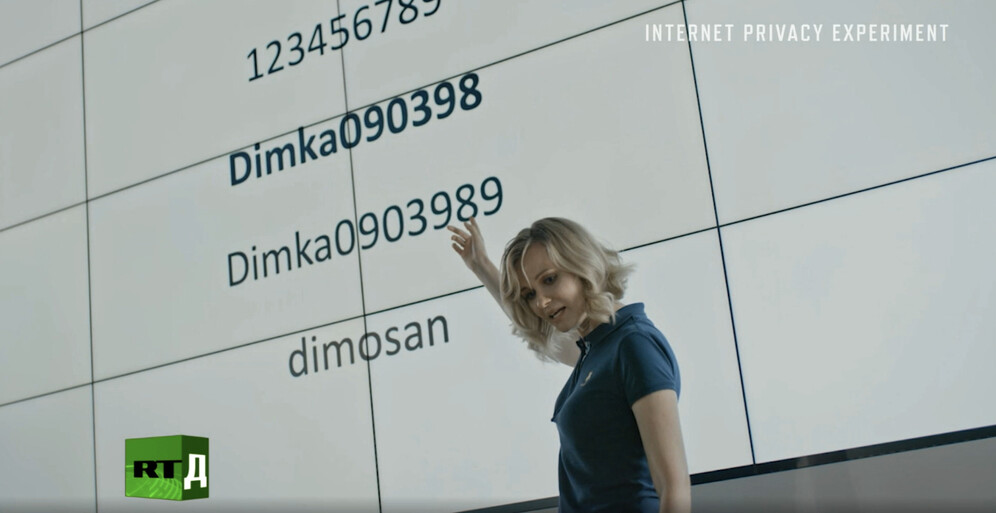
"If I show you your passwords and all the data I could get within minutes, including your address and the contacts you call most often, it will be much harder for you to say 'So what?'. Because though all these look like mere numbers and letters, these numbers and letters turn out to be the key to your thoughts that can be used as a hook to trick you," says Anna Kulik, profiler and president at the Research Institute of Corporate Security.
Simply put, all your personal data available online can be used to manipulate your behaviour.
Playing up your emotions
"They play to human emotions," says Hadi Hosn, CEO at Axon Technologies. "They play to the emotions of urgency, to the emotion of promising something, so excitement, they play to the emotion of less carefulness - when you look at things and just clicking because you recognise a brand or an image. And they try to make users provide as much personal information as they can."

Means and methods employed by hackers to play to people's feelings and emotions vary greatly. However, all of them are referred to as social engineering, i.e. malicious activities perpetrated through social interactions. The main thing about social engineering is that it employs psychological manipulation to trick users into making security errors and revealing sensitive information.
What makes social engineering particularly dangerous is that it depends on human error rather than software vulnerabilities. Unfortunately, human mistakes are much less predictable, making them much harder to identify and eliminate than malware-based attacks.
One of the essential feelings that hackers tend to play up is trust. To do so, they collect as much information about a user as possible and show the user how well they know them.
"Once the attackers collect that information, they can then craft more focused attacks on that user. For example, the database leak has a name; it has potentially even the address of that person. It potentially also has a view of where they've been in the last six months," says Hadi Hosn, CEO at Axon Technologies. "So now if he creates a phishing attack on that individual, he can say: 'We know you live at this address. We know you go to this work'. And that's building trust."
Another human emotion that cybercriminals cruelly employ is fear.
According to Robert Plutchik, a pioneer in the psychology of emotion, fear is among the most powerful emotions experienced by human beings. Consequently, fear is of extreme importance when it comes to our decision-making and behaviour. Furthermore, it has been scientifically proven that it profoundly impacts people's judgement and choices when the emotion is triggered. As a result, fear-appealing hacker attacks seem to be among the most effective.

"They said I was kidnapped, or that I was injured, or something like that," says Sam Suchet, development director at EEC Services, who has witnessed a fear-appealing cyber attack against one of his dearest and nearest. "It's very real. The sophistication is incredible. It's very difficult for people to understand where the email came from, what domain it's associated with. So, if Google is not picking it up as spam, or your mail app is not picking it up as spam, you'd better think twice before opening it and say to yourself: 'Ok, this looks suspicious. Let me double-check with Sam and make sure whether he has really been kidnapped'."
The art of hacking
Apart from simply using your data to trick you, cyber wrongdoers can use your digital footprint to hack your accounts and get access to even more sensitive data like private messages, the use of which automatically amplifies their capabilities of playing to your fear.
"That is, for example, let's say we make a separate web page, which will be very similar to the home page of a social media. We'll send you private messages – from a hacked account of your friend and say: 'Bro, everything is very bad. A video from our party has been leaked. We need to do something about it," contemplates Gleb Mihkeev, technical director at Beta Digital Production. "That is, we will catch you in a fright – you will click on the link, you will see your social media page there, which is unauthorised. You'll say, 'Damn, for some reason, I was unauthorised'. Then you'll enter your username and password without a second thought. And yes, probably after that, you will even get the video back."
Another means hackers employ to get hold of your sensitive information is creating a backdoor. This vulnerability allows them to get access to data or to gain remote control over a device. It can work in different ways. For example, you can correspond with someone in a chat, say a nice girl or a nice guy. They'll send you a photo, and you'll, of course, open it. But the fact is that a backdoor may be "stuck" to the image.

"You create a backdoor. It is not very easy to promote it, but when it is promoted, then you get just everything – access to the camera at any time, access to calls, messages, applications, and so on. It's really cool, it's great," says a real-life hacker interviewed by RT Documentary. "No matter how absurd it may sound, most of our users are really like this. And that's it, and you get access to personal messages, all media files, yes, that is, text, correspondence etc.… That is a fairly classic story."
Building up the defence
Though all these stories may seem quite depressing, there's no need to fall into despair and throw away all your gadgets. After all, remember all the possibilities the world wide web opens before us.

However, it would help if you were prepared to organise a defence and stand up for your security online.
"Yes, they should, probably…" says Gleb Mikheev commenting on the incident. "If they're really worried about it. The question you always need to ask yourself is what aspects of your online activity can be leaked and used against you".

To learn more about hackers playing our emotions, tune in to the premiere of the third episode of I Am Hacked on Monday!